Welcome to Gaming4Free, where you can host your Minecraft server for free. Have fun in the blocky world of Minecraft without worrying about money. We make sure your game runs super smooth, and we have a cool community.Gaming4Free is for everyone, whether you're a Minecraft pro or just starting out. We believe games should be free, and we're here to help you have a great time in Minecraft.
Use StegSolve to browse through different bit planes of the image to find hidden text. 5. The Flag
If the archive is locked and no hint was provided in the challenge description, attackers typically use John the Ripper or Hashcat . Use rar2john 19977.rar > rar.hash . Crack the hash: Use a wordlist like rockyou.txt . john --wordlist=rockyou.txt rar.hash Use code with caution. Copied to clipboard 4. Steganographic Analysis
Extract the hidden flag or data contained within the encrypted/obfuscated RAR archive. Step-by-Step Analysis 1. Initial Identification
You may see a file named flag.txt or a nested image (e.g., hint.png ). If the file listing is encrypted, you will need a password immediately. 3. Password Recovery (Brute Force)
HxD (for checking file headers like 52 61 72 21 ).
Once decrypted or extracted, the final step is usually finding a string in the format CTF{...} or FLAG{...} . Extraction: 7-Zip or Unrar . Cracking: John the Ripper.
Gaming4Free's control panel is like your gaming dashboard. It's super easy to use and lets you take charge of your game server. You can do things like add cool mods and change settings with no fuss. It's all about giving you control, so you can enjoy your gaming without any hassles.
 Realtime Console
Realtime Console File Management
File Management Automatic Version Installer
Automatic Version Installer Unlimited Players
Unlimited Players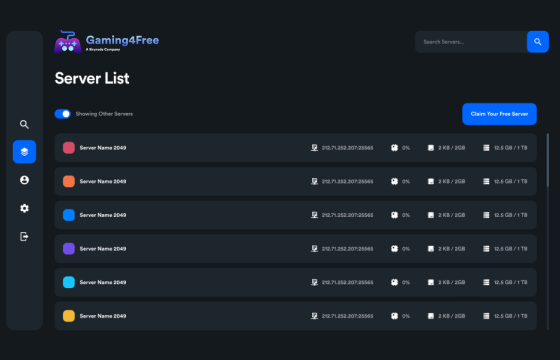

We empower your creativity with free game hosting. Whether you're crafting epic adventures or building worlds of your own, our hosting lets your imagination soar without the cost. Join us today and transform your gaming dreams into reality with Gaming4Free.

Use StegSolve to browse through different bit planes of the image to find hidden text. 5. The Flag
If the archive is locked and no hint was provided in the challenge description, attackers typically use John the Ripper or Hashcat . Use rar2john 19977.rar > rar.hash . Crack the hash: Use a wordlist like rockyou.txt . john --wordlist=rockyou.txt rar.hash Use code with caution. Copied to clipboard 4. Steganographic Analysis 19977.rar
Extract the hidden flag or data contained within the encrypted/obfuscated RAR archive. Step-by-Step Analysis 1. Initial Identification Use StegSolve to browse through different bit planes
You may see a file named flag.txt or a nested image (e.g., hint.png ). If the file listing is encrypted, you will need a password immediately. 3. Password Recovery (Brute Force) Use rar2john 19977
HxD (for checking file headers like 52 61 72 21 ).
Once decrypted or extracted, the final step is usually finding a string in the format CTF{...} or FLAG{...} . Extraction: 7-Zip or Unrar . Cracking: John the Ripper.