Lhfs_1zip ✧
Creating a symlink inside the archive that points to a sensitive system file. When the service "updates" or "reads" the file, it interacts with the system target instead. 3. Exploitation (General Example)
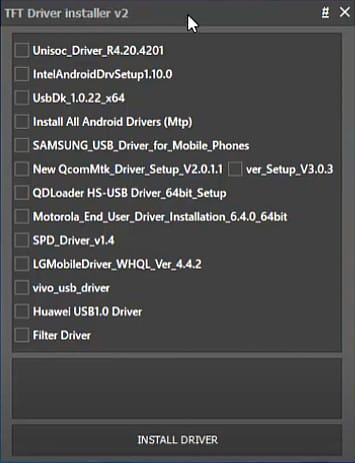
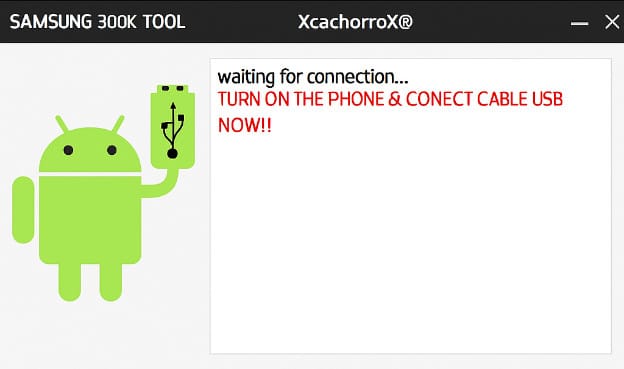
The "lhfs" component suggests the challenge interacts directly with the host's file system. Common attack vectors include: lhfs_1zip
A service or binary that parses a custom archive format called .1zip . Creating a symlink inside the archive that points
The first step in these challenges is usually reverse-engineering the .1zip header. Typically, the format includes: A sequence (e.g., 1ZIP ). Metadata for file count and individual file lengths. Filenames followed by the raw File Content . 2. Identifying the Vulnerability Typically, the format includes: A sequence (e
If the goal is to read a flag located at /flag.txt , the exploit usually involves crafting a malicious .1zip file: Manually create a file with the 1ZIP header. Payload: Set the filename field to ../../../../flag.txt .









Post Comment