Rdp Recognizer.zip File
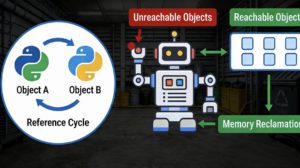
: Tools like this exploit common RDP weaknesses, such as weak or default credentials and unpatched system vulnerabilities (e.g., BlueKeep ).
If you are investigating RDP activity, you might also encounter these similar tools or terms: Puzzling RDP Cache - Putting the Pieces Together RDP Recognizer.zip
: It is often distributed or found in investigative logs as a compressed file, such as RDP Recognizer.zip . Related RDP Tools & Forensic Artifacts : Tools like this exploit common RDP weaknesses,
: It identifies accessible RDP services within a network and attempts to gain unauthorized access by testing various password combinations (brute-forcing). is a specialized cyber tool used for brute-forcing
is a specialized cyber tool used for brute-forcing RDP passwords and scanning for vulnerabilities in Remote Desktop Protocol (RDP) services. While it can be used for security testing, it is prominently categorized as a threat actor tool. Key Details & Security Context
: U.S. authorities have observed the BianLian Ransomware Group using RDP Recognizer during their network intrusions to facilitate lateral movement.