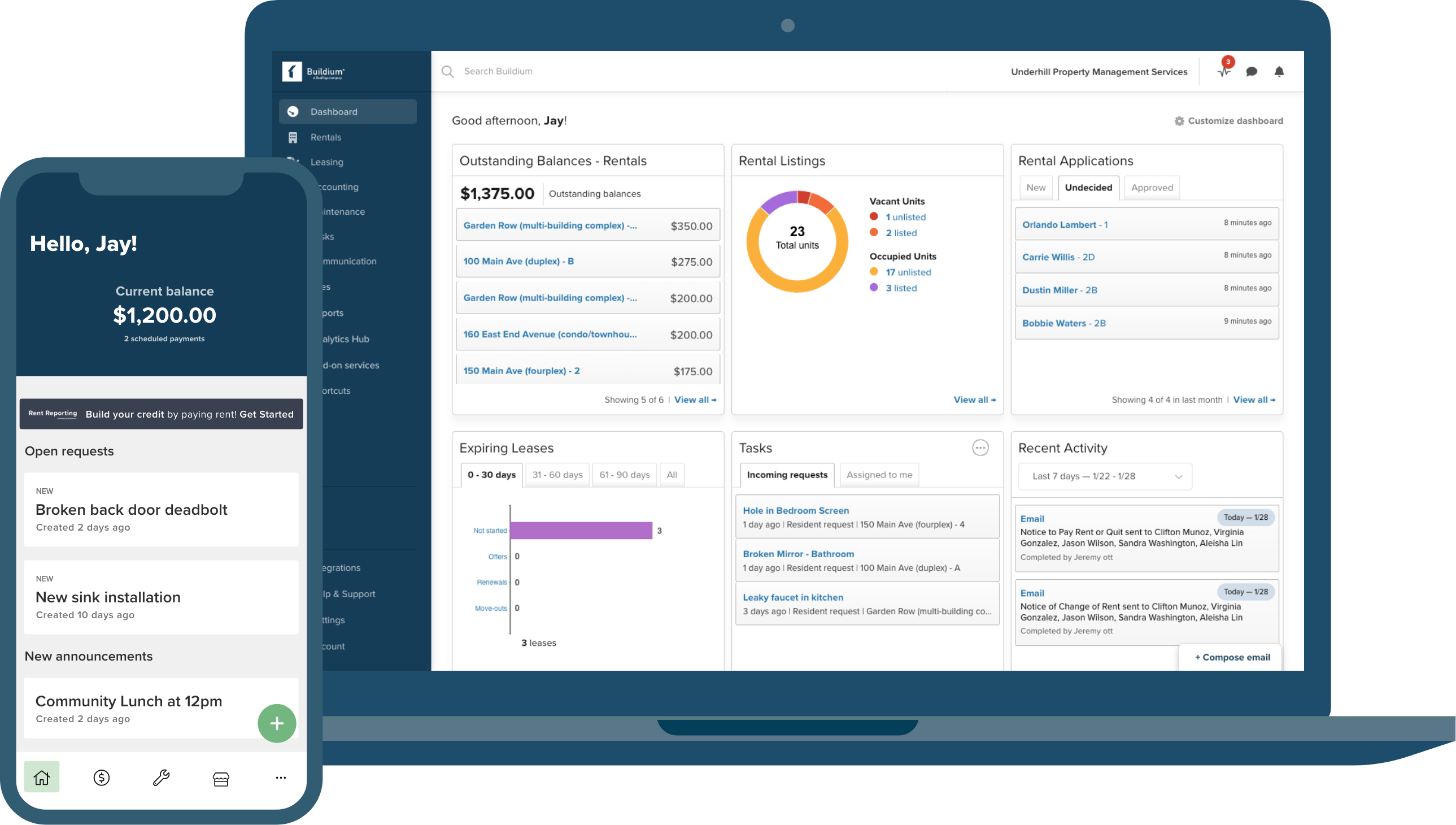
Every feature. All in one platform.
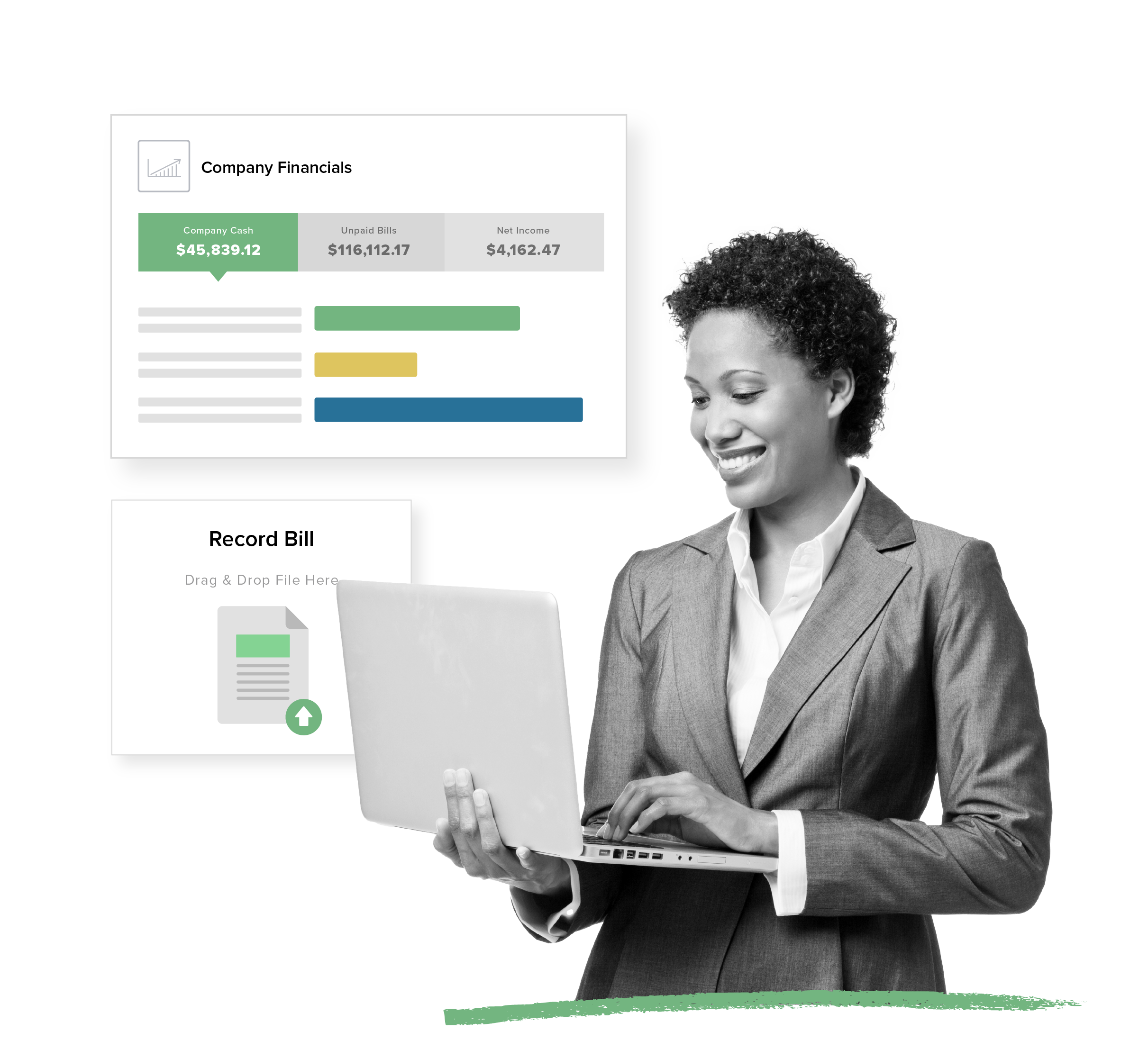
Purpose-Built Accounting
Get the guided workflows and automations made for property management that non-accountants want with the depth pros demand.
- Automatic bank reconciliation
- 1099 e-filing in minutes
- Property-specific financial reporting
View Accounting Features
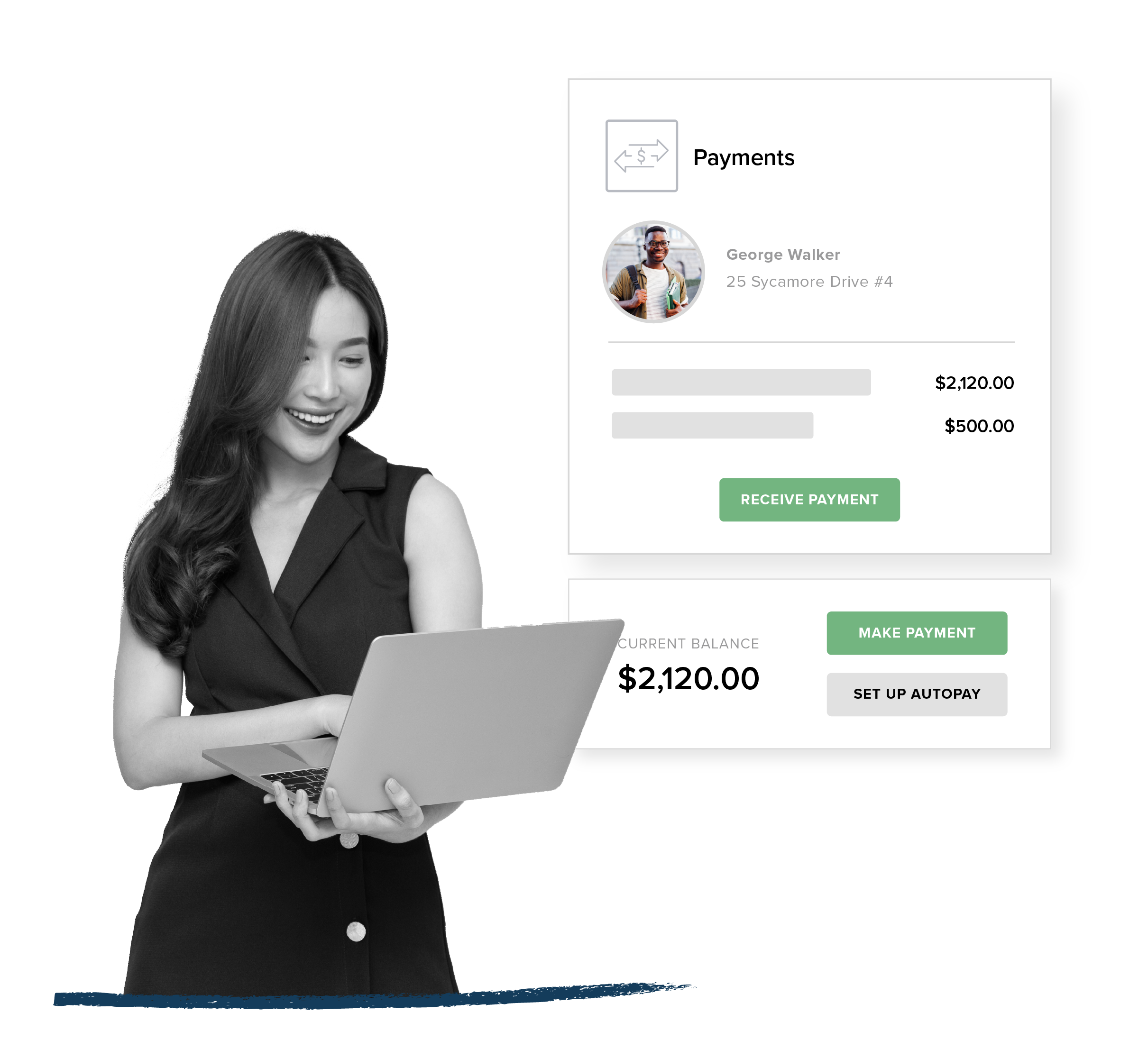
Rent Collection
Automate payments for your residents, owners, and vendors while opening up new revenue streams inside your portfolio.
- Convenient online rent and bill payments via ACH and credit card
- Funds automatically transferred to your bank account
- Optional transaction fees cover your costs or generate extra revenue
View Payments Features
Listing + Leasing
Offer online leasing that fills vacancies fast and delights incoming residents.
- One-touch syndication to market your listings across top rental sites
- Seamless online rental applications with built-in tenant screening services
- 100% digital, paper-free leasing process
View Leasing Features
The Best Property Management Apps
Serve up the smoothest experience with top-rated mobile apps that put your communication on point with residents and owners.
- Highly rated property manager and Resident Center apps
- On-the-go connectivity for faster response times
- Self-service options that reduce calls and emails
View Features
Industry-Leading Integrations
Centralize and build out your tech stack through an ecosystem of leading integrations in Buildium Marketplace.
- Proven apps from leading proptech partners
- No monthly subscriptions (pay as you go)
- Links right into your Buildium account
Discover Marketplace
Made for mixed portfolios
Sbornik Programm Dlia Vzloma Skachat 【iOS EXCLUSIVE】
If you are interested in how these programs work, the best way to learn is through legitimate, "white-hat" resources that provide safe environments for testing.
: Use verified Ethical Hacking Resources to learn the theory behind vulnerabilities rather than just running automated "vzlom" scripts.
: Many of these collections include hidden miners that use your CPU and GPU power to mine cryptocurrency for the attacker. 2. Legal and Ethical Consequences
: There is a massive difference between "hacking" (unauthorized access) and "ethical hacking" (improving security). Using unverified "collections" falls into the former and lacks the professional standards of the Ethical Hacking community . 3. Safer Alternatives for Learning
While the curiosity to explore cybersecurity tools is common, these specific "all-in-one" bundles found on forums or file-sharing sites are frequently "backdoored" by the people who created them. 1. The Trojan Horse Effect
: Tools like keyloggers, remote access trojans (RATs), and stealers are often hidden within the software. When you run a tool to "hack" something else, it silently infects your own machine first.
95% Customer Support Satisfaction Rating
Success is our
middle name (literally)
Our Customer Success Team has spent years perfecting our renowned customer service model. From the moment you begin onboarding, your business is our sole focus.
- Reliable, live phone support in minutes (not hours)
- 85% of customer support calls are resolved on the first call
- 34% increase in support agent staffing since 2024
Customer CareOnboarding

Need an app? Add it in a snap.
Buildium Marketplace gives you on-demand access to the latest property management tools and platform integrations – from a growing roster of leading proptech partners.
Select Buildium Marketplace integrations:
If you are interested in how these programs work, the best way to learn is through legitimate, "white-hat" resources that provide safe environments for testing.
: Use verified Ethical Hacking Resources to learn the theory behind vulnerabilities rather than just running automated "vzlom" scripts.
: Many of these collections include hidden miners that use your CPU and GPU power to mine cryptocurrency for the attacker. 2. Legal and Ethical Consequences
: There is a massive difference between "hacking" (unauthorized access) and "ethical hacking" (improving security). Using unverified "collections" falls into the former and lacks the professional standards of the Ethical Hacking community . 3. Safer Alternatives for Learning
While the curiosity to explore cybersecurity tools is common, these specific "all-in-one" bundles found on forums or file-sharing sites are frequently "backdoored" by the people who created them. 1. The Trojan Horse Effect
: Tools like keyloggers, remote access trojans (RATs), and stealers are often hidden within the software. When you run a tool to "hack" something else, it silently infects your own machine first.